How a Simple Phishing Mistake Can Cripple an Organization
In today’s digitally connected environment, many cyber incidents begin with something that appears harmless – a single click on an email link. What looks like a routine message from a colleague, bank, vendor, or manager may actually be a carefully crafted phishing attack, with artificial intelligence it gets more sophisticated. Within seconds, that one click can open the door to a chain of events capable of disrupting business operations, exposing sensitive information, and causing serious financial losses. Allen was there! See the book on the footnote below!
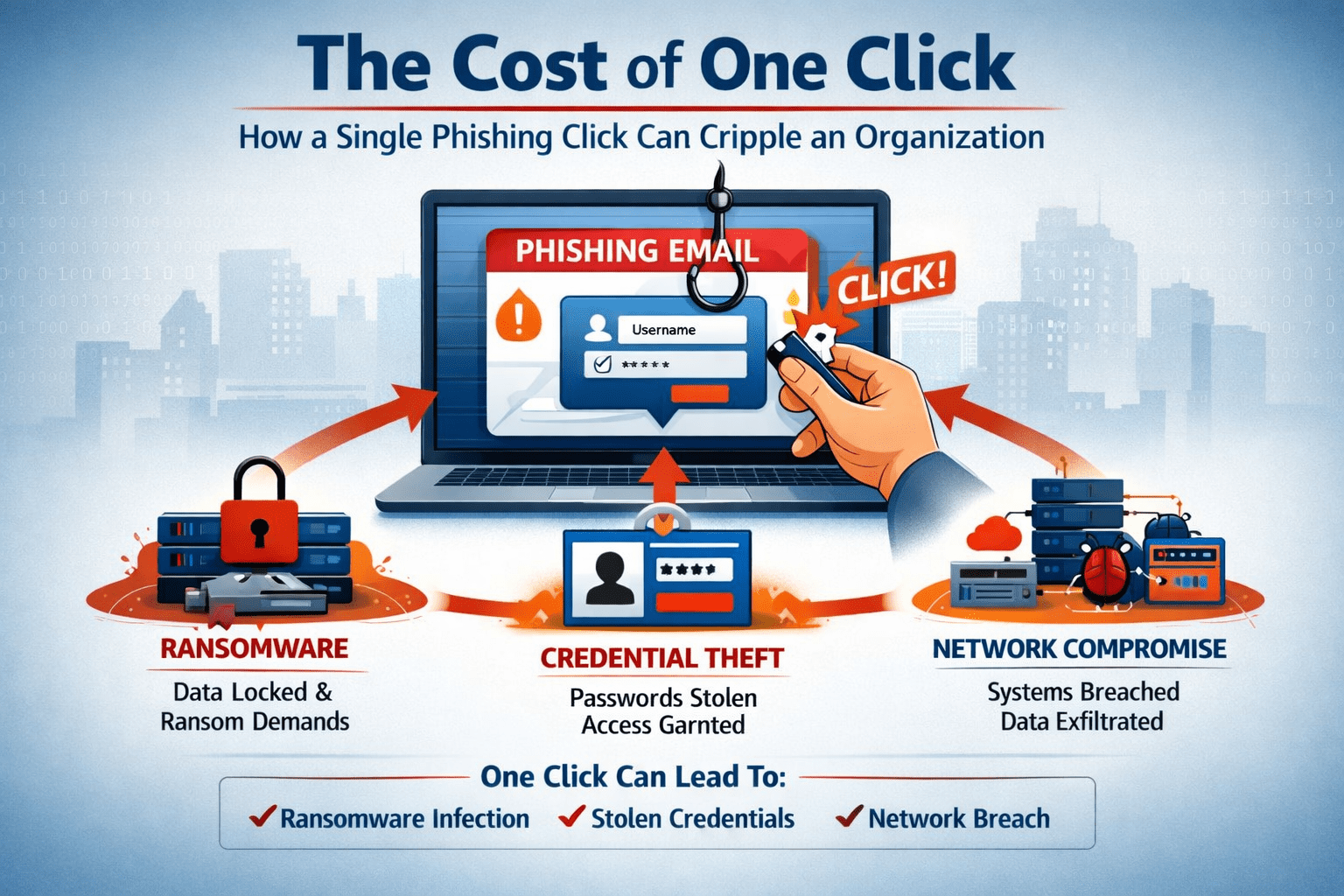
Phishing remains one of the most effective attack methods used by cybercriminals because it targets human trust rather than technological weaknesses. When an employee clicks a malicious link or downloads an infected attachment, the consequences can extend far beyond that single action. Three major threats often follow: ransomware infection, credential theft, and network compromise.
Ransomware: When One Click Locks an Entire Organization
Ransomware attacks frequently begin with phishing emails. A malicious attachment or deceptive link may install hidden software on the victim’s computer without their knowledge. Once activated, the ransomware begins encrypting files across the system and sometimes across the entire organizational network.
The impact can be devastating. Critical business documents, operational data, financial records, and customer information may suddenly become inaccessible. Attackers then demand payment in exchange for the decryption key needed to restore access to the data.
Beyond the ransom demand itself, organizations often face additional costs including system recovery, operational downtime, legal exposure, and reputational damage. In many cases, the origin of the incident can be traced back to a single employee who unknowingly interacted with a malicious email.
Credential Theft: Giving Attackers the Keys to the System
Another common outcome of phishing attacks is credential theft. In this scenario, the victim is directed to a fake login page designed to imitate a legitimate platform such as corporate email, cloud storage, or banking services. Believing the page to be authentic, the user enters their username and password.
The attacker instantly captures these credentials.
With valid login information, cybercriminals can access internal systems without raising immediate suspicion. They may read confidential emails, steal sensitive documents, impersonate executives, or initiate fraudulent financial transactions.
Credential theft is particularly dangerous because it allows attackers to operate inside the organization’s digital environment while appearing to be legitimate users. By the time suspicious activity is detected, significant damage may already have occurred.
Network Compromise: Expanding the Breach
A successful phishing attack rarely stops at a single device. Once attackers gain access to one system, they often attempt to move deeper into the network. This process, sometimes referred to as lateral movement, enables them to explore other computers, servers, and databases within the organization.
Through this expanded access, attackers may deploy additional malware, extract sensitive corporate data, or establish persistent backdoors that allow them to return even after the initial breach is discovered.
Network compromise can disrupt operations on a large scale. Critical systems may be disabled, confidential information may be exposed, and the organization’s digital infrastructure may require extensive rebuilding to restore security.
Why Phishing Continues to Succeed
Despite advances in cybersecurity technology, phishing attacks remain effective because they exploit human behavior. Attackers commonly design their messages to create urgency, curiosity, or authority. Emails may appear to come from senior executives requesting immediate action, from banks warning of suspicious transactions, or from service providers asking users to verify account information.
When employees respond quickly without verifying the authenticity of the message, the attacker’s objective is achieved.
Technology alone cannot fully solve this problem. Human awareness and vigilance remain essential components of effective cybersecurity defense.
Building a Culture of Phishing Awareness
Organizations that successfully reduce phishing risks invest in continuous security awareness training. Employees must be able to recognize suspicious emails, verify unexpected requests, and understand the potential consequences of interacting with unknown links or attachments.
Practical steps include:
- Encouraging employees to verify unusual requests through separate communication channels
- Promoting a “pause before you click” culture when dealing with unexpected emails
- Conducting periodic phishing awareness training and simulations
- Establishing clear procedures for reporting suspicious messages
When employees are trained to recognize phishing indicators, the likelihood of costly security incidents can be significantly reduced.
The Human Firewall
Every organization invests in digital security tools such as firewalls, antivirus systems, and intrusion detection technologies. However, the most important line of defense is often the human one. Employees who understand phishing risks become a powerful protective layer against cyber threats.
Cybercriminals rely on one small mistake – a single click – to begin their attack. But with proper awareness and vigilance, that click can be avoided.
The security of an organization is not determined solely by the sophistication of its technology, but by the awareness of the people who use it.
For organizational leaders, security professionals, and individuals seeking a deeper understanding of phishing threats and how they unfold in real-life scenarios, these concepts are explored further in the book Phishing Awareness.
See the links to online store for the book purchase.